How a Milwaukee Small Business Recovers From a Ransomware Attack
For any Milwaukee small business owner who has not yet thought seriously about cybersecurity, the story that follows is worth reading slowly. Small business cybersecurity in Milwaukee is not a niche concern for tech companies or large enterprises. It is a ground-level operational risk that accountants, retailers, contractors, and medical offices face every single week, and the businesses that recover well are almost always the ones that prepared before anything went wrong.
Monday Morning on the West Side
It is 8:15 on a Monday morning at a small accounting firm on Milwaukee’s west side. The office manager arrives first, sets down her coffee, and wakes up her workstation. The screen that loads is not her desktop. It is a ransom note. Every file on the network has been encrypted. Client tax returns, payroll records, QuickBooks data, scanned documents going back six years — all of it is locked behind a key controlled by someone in another country who is asking for $18,000 in cryptocurrency to give it back.
She calls the owner. He calls his cell phone carrier, thinking somehow this is a phone problem. Then he calls his nephew who is good with computers. By 10:00 a.m., they know enough to understand this is serious. By noon, they have unplugged everything they can think to unplug. The phones are still ringing with clients calling about their returns.
This is not a hypothetical constructed to scare you. This is a composite of real events happening to real Milwaukee businesses. The FBI’s Internet Crime Complaint Center reported that ransomware remains one of the most financially damaging cyberthreats facing small and medium businesses, with thousands of complaints filed annually across every industry sector. The accounting firm on the west side is not an outlier. It is the norm.

What the First 72 Hours Actually Look Like
The first three days after a ransomware attack with no IT plan in place are defined almost entirely by decisions made under pressure without enough information. That combination is expensive.
The immediate priority is isolation. Every device still connected to the network needs to come off it, which means disconnecting from Wi-Fi, pulling ethernet cables, and shutting down network-attached storage. The goal is to stop the encryption process from spreading to systems it has not yet reached. In a small office with shared drives and cloud sync enabled, this is harder than it sounds. Cloud-synced folders can push encrypted versions of files upstream before anyone realizes what is happening, which means the backup you thought you had may now contain encrypted garbage.
CISA’s ransomware guidance emphasizes that victims should not turn off affected machines immediately, as powered-on systems may retain volatile memory evidence useful for forensic investigation. This is counterintuitive for most people. The instinct is to pull the plug. The right move is more deliberate, and without someone who knows what they are doing, most small business owners will make the wrong call.
Then comes the ransom decision. Paying does not guarantee recovery. Verizon’s Data Breach Investigations Report has consistently found that small businesses represent a disproportionate share of breach victims, and ransomware figures prominently as an attack pattern across industries with limited security resources. Some businesses pay and receive a working decryption key. Others pay and receive nothing, or receive a key that only partially works. The FBI recommends against paying, and doing so may carry regulatory implications depending on whether the attacker group is on a sanctions list. For the accounting firm, paying means potentially funding a sanctioned entity. Not paying means rebuilding from scratch. Neither option is good.
Meanwhile, the billable hours stop. For an accounting firm in tax season, a single week of downtime can represent tens of thousands of dollars in lost revenue. Clients are calling. Some of those clients have sensitive financial data sitting on the encrypted server, which means there may be notification obligations under Wisconsin’s data breach law and, depending on the client mix, under federal regulations as well. The owner is now managing a technology crisis, a client relations crisis, and a potential regulatory exposure simultaneously, with no IT partner and no documented response plan.
Walking Through Recovery
Assuming the decision is made not to pay, recovery begins with a clean assessment of what is actually gone. This means bringing in a qualified IT professional to determine which systems were encrypted, whether any data was exfiltrated before encryption, and whether the attacker left any backdoor access on the network. Rebuilding on a compromised network is not recovery. It is an invitation for the same thing to happen again in three months.
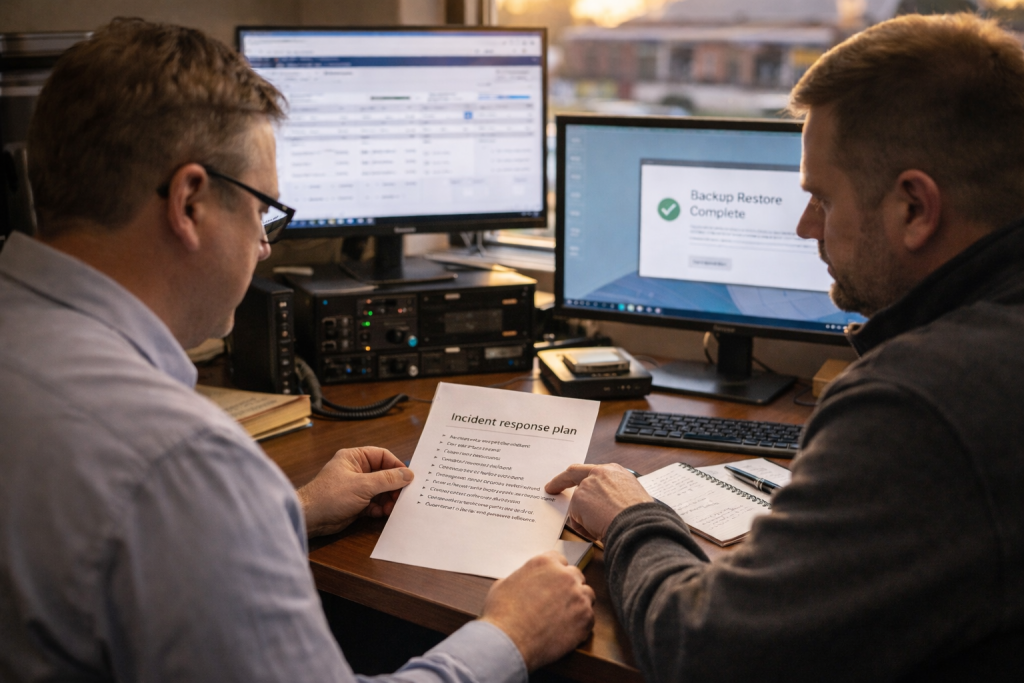
If verified backups exist and were stored offline or in an isolated environment that the ransomware could not reach, restoration is painful but straightforward. The timeline depends on the volume of data and the speed of the recovery infrastructure, but a business with clean backups and a competent IT partner can often restore core operations within 24 to 72 hours. The SBA’s cybersecurity resources note that maintaining tested, offline backups is one of the most critical and cost-effective defenses available to small businesses.
If no usable backup exists, the path is harder. Systems need to be wiped and rebuilt from the operating system up. Applications need to be reinstalled and reconfigured. Data that was not backed up is gone unless a decryption key is obtained. Some businesses in this position recover most of their data by piecing together email archives, client-submitted documents, and paper records. Others accept permanent data loss. The outcome depends entirely on what was in place before the attack.
Once systems are restored, the incident needs to be documented thoroughly for insurance purposes. Cyber liability insurance claims require detailed records of what happened, when it happened, what was affected, and what recovery steps were taken. A business that cannot produce this documentation may find its claim denied or reduced. Filing a report with the FBI’s IC3 complaint center is also recommended and costs nothing.
What to Have in Place Before It Happens
The businesses that recover fastest from ransomware share a short list of common characteristics. They have verified, working backups stored in a location the ransomware cannot reach, tested regularly enough that someone actually knows they work. They have endpoint protection on every device that connects to the network, not just the main workstations. They have multi-factor authentication enabled on every account that holds sensitive data or provides remote access to the network. And they have a local IT partner who knows their environment and can respond within hours, not days.
None of this is complicated in concept. The challenge for most small business owners is that setting it up correctly requires expertise they do not have in-house, and the urgency never feels real until the Monday morning screen shows a ransom note instead of a desktop.
A documented incident response plan does not need to be a 40-page binder. It needs to answer four questions: who do you call first, what do you shut down immediately, who are the clients or regulators you must notify, and where are the backups. A single page with clear answers to those four questions, reviewed once a year with your IT partner, changes the trajectory of a ransomware event dramatically.
RedBird Handles This Before It Becomes a Crisis
If you are a Milwaukee-area small business owner and your current answer to “what happens if ransomware hits us tomorrow” is “I don’t know,” that is the gap worth closing today. Our [managed IT services] [link to managed IT services page] include proactive monitoring, verified backup management, endpoint protection, and MFA deployment across your environment. Our [cybersecurity support] [link to cybersecurity services page] is designed specifically for small businesses that need enterprise-level protection without the enterprise-level overhead. And because we are local, when something goes wrong, we show up.
For small business cybersecurity in Milwaukee, the window between “we should probably look into this” and “we have a serious problem” closes faster than most owners expect. A free consultation costs you an hour. A ransomware event with no plan in place costs far more than that.
Call us at (262) 475-2615 or visit our website to schedule your free consultation. RedBird Technology Solutions serves businesses throughout Milwaukee, Wauwatosa, West Allis, Brookfield, Shorewood, and the surrounding communities. Let’s make sure your business is ready before Monday morning looks like the scenario above.
