Is Your Business Email Already Compromised?
Is Your Business Email Already Compromised?
The FBI now tracks over $2.8 billion in annual losses to a single attack that leaves no malware, no alarms, and no warning signs. Here is what every Milwaukee business owner needs to know right now — and the four steps that actually stop it.
Most break-ins look like break-ins. A window gets smashed. An alarm sounds. Someone notices. Business Email Compromise does none of that. The attacker walks in through the front door using credentials that were already sitting in your inbox, and by the time anyone figures out something went wrong, the money is already gone.
A law firm partner forwards a real estate closing email to their paralegal. The wire instructions look just like last month’s. Same format. Same professional tone. Even the same signature block at the bottom. The paralegal processes the wire. The instructions were not last month’s.
$400,000 was gone before anyone picked up the phone. No hack. No malware. No system alert. Just a quiet inbox takeover that had been sitting undetected for weeks, watching and waiting for exactly the right moment.
That is not a rare story. It is the playbook. And in 2026, it has become the single most costly financial cyber threat facing professional services businesses across the country — including right here in Milwaukee.
What Business Email Compromise Actually Is
This is not the scam email from a foreign prince that everyone learned to ignore twenty years ago. Business Email Compromise — BEC — is a slow, patient, surgical attack. The criminal gains access to a real inbox, usually a partner, an owner, or a controller, and then does nothing right away. They read. They watch. They learn how you write, who you trust, and what a normal wire transfer request looks like at your company.
Then, at exactly the right moment during a real, live transaction, they step in. One email with updated wire instructions. Everything about it looks right and feels right because it came from inside the actual thread, or from an address one character off from the real one. The request gets honored. The funds move. The attacker disappears.
What makes this so dangerous is precisely what makes it hard to catch: there is no malware to detect, no phishing link to flag, and no unusual login to trigger an alert. The FBI’s Internet Crime Report puts annual U.S. BEC losses at $2.8 billion. Legal, healthcare, wealth management, and CPA firms sit at the top of the target list because that is where the money moves.
Milwaukee Businesses at the Top of the List
Attackers go where the money moves under time pressure. They are not random. The businesses they hit hardest are the ones handling client funds, real estate closings, legal fees, insurance settlements, or large vendor invoices. If your company moves money and communicates primarily by email, you are in the cross-hairs.
Law Firms
Wire transfers at closing, trust accounts, and settlement payments. Large dollar amounts and tight deadlines create exactly the high-pressure conditions attackers rely on.
CPA & Financial Firms
Tax season wire activity, client fund management, and retirement account transfers. The trust relationship between accountant and client makes requests feel safe.
Healthcare Practices
Insurance billing, large vendor payments, and payroll. A staff of fifteen with variable email habits gives attackers multiple potential entry points into the same organization.
Construction & Real Estate
Large project invoices and property closings represent exactly the kind of high-value, time-pressured transactions that make BEC so lucrative for attackers.
The Four Stages of a BEC Attack
Understanding the exact playbook is your first real line of defense. Once you see it, you cannot unsee it. And once your staff sees it, they start asking the right questions before wiring a single dollar.
Initial Access
The attacker gets into a mailbox — usually through a phishing link, a reused password exposed in an old data breach, or a weak credential with no multi-factor authentication on it. No forced entry. No alert. They are simply in.
Silent Surveillance
For days or weeks, they read your threads. They learn your tone, your vendors, your clients, and your financial workflows. They set up silent forwarding rules inside the mailbox so every new email continues to copy to them, even after a password change.
The Strike
During a live, real transaction, they step in with one email. New wire instructions. The message lands inside an actual thread, carries the right context, and sounds exactly like the person it is pretending to be from. Because it came from inside the conversation.
Funds Transfer and Disappear
The money moves before anyone questions it. Wire transfers are notoriously difficult to reverse once processed. Recovery rates are low. Most businesses absorb the loss entirely, and many never report it publicly.
The typos and broken grammar that used to make phishing emails easy to spot are gone. Attackers now use AI tools that produce flawlessly professional, perfectly toned emails that mirror your colleagues’ actual writing styles. The old advice of “just look for bad spelling” does not protect you anymore. Your first line of defense has to be process, not pattern recognition.
The attacker sits in a partner’s mailbox for weeks, reads the threads, learns the voice, then steps in at closing with new wire instructions. No malware. No alarms. Just silence, then money gone.How a BEC attack unfolds in 2026
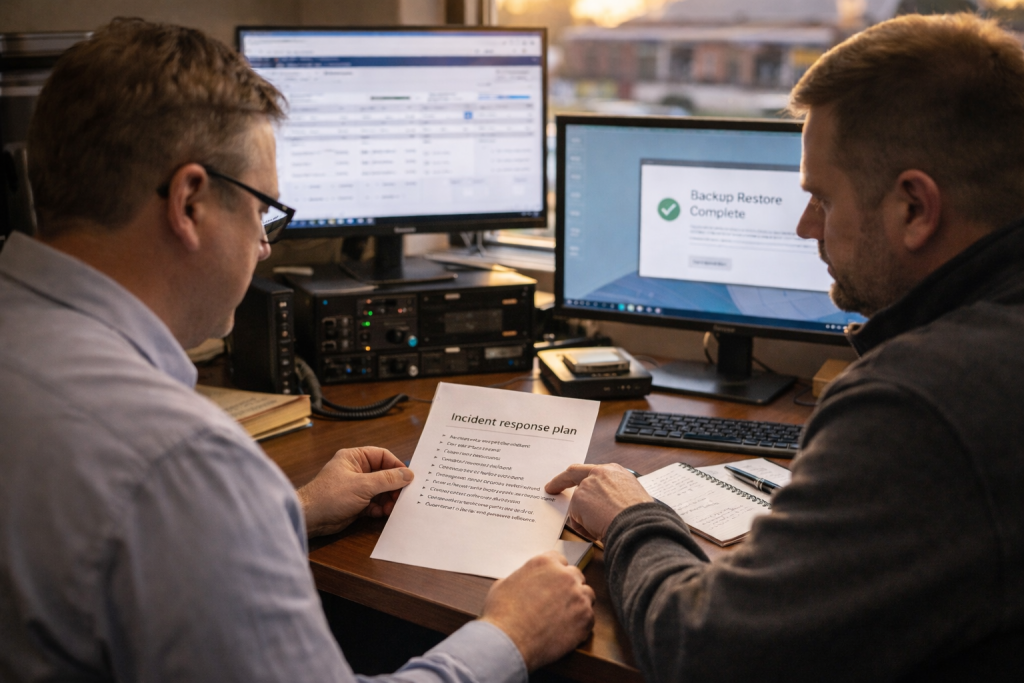
What Actually Stops a BEC Attack
The good news is that this threat is very defendable. The reason most Milwaukee businesses are not protected is simply that nobody has ever sat down and configured these controls properly. They are not complicated. They just need to be done — and then maintained. Here is exactly what works.
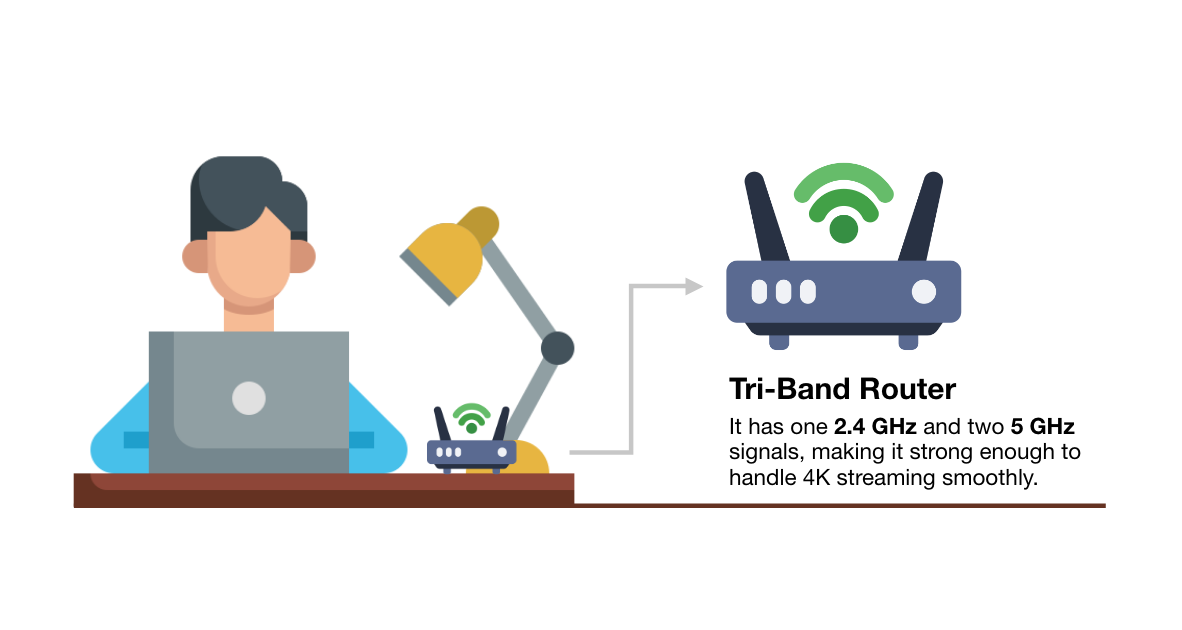
Multi-Factor Authentication on Every Inbox and Every Device
MFA means that even if a password is stolen or exposed in a breach, the attacker still cannot get into the mailbox without a second verification step. This is non-negotiable. If your Microsoft 365 or Google Workspace accounts are not protected by MFA right now, this is the first thing to fix.
Conditional Access Policies Configured Correctly
Properly set up, these flag and automatically block logins from impossible travel patterns and unfamiliar geographic locations. Most small businesses have Microsoft 365 licenses that include this capability and have never turned it on.
Mailbox Forwarding Audits Every Single Month
Attackers plant silent forwarding rules inside compromised mailboxes so every email continues to copy to them indefinitely, even after you change the password. These need to be reviewed monthly by someone who knows exactly what a clean mailbox looks like.
The Wire Verification Rule — Written Down and Enforced
Any change to wire transfer instructions gets verified by a live phone call to a number already in your file — never a number from the email itself. Write this down. Make it a hard policy. This single step stops BEC cold even when everything else has already failed.
We also recommend tabletop exercises — short, guided walk-throughs where your team practices responding to a wire fraud attempt in real time. They take about an hour and they change how your staff thinks. If your last one was more than a year ago, your cyber insurance carrier is likely going to have questions at your next renewal.
Most Milwaukee businesses we talk to already have Microsoft 365 licenses that include MFA, Conditional Access, and audit logging. The tools are already paid for. They just have never been configured. A single afternoon of proper setup closes the most common BEC entry points immediately.
The Difference a Milwaukee Provider Makes
There is a version of IT support that works like a call center. You dial in, explain your situation to whoever picks up, get walked through a script, and either resolve the issue or get escalated to someone else who makes you explain it again from the beginning. That model exists because it is cost-efficient for the provider. It is also genuinely frustrating when you are dealing with something as time-sensitive as a potential email breach, and the person on the other end has never been in your building, does not know your setup, and is working from notes rather than experience.
RedBird has been supporting businesses across the Milwaukee area for over twenty years. Every technician who comes to your location is a direct RedBird employee — not a subcontractor dispatched from a third-party network, not a rotating temp filling a coverage gap. The same people show up, they know your environment, and they are accountable to the same company you called. Our staff is also bilingual, which in a community as diverse as greater Milwaukee is a practical advantage, not a footnote.
When something like a BEC attempt happens, the difference between a local provider who already knows your Microsoft 365 environment and a national helpdesk that is seeing your setup for the first time is the difference between a contained incident and a wire transfer that does not come back.
If your last security review was more than a year ago — or if you have never had one — your email environment almost certainly has gaps you are not aware of. Not because someone made a mistake, but because this threat moves fast and most small businesses are simply running on defaults that were never designed to stop something like this.
We will come in, review your current setup, show you exactly where the exposure is, and give you an honest recommendation with no obligation and no sales pressure. That is how we have built our reputation in this market for over twenty years, and it is not something we are going to change.
Find Out If Your Email Is Already at Risk
We will review your setup, identify the gaps, and give you a straight answer. Free consultation. No pressure. No obligation.
Schedule Your Free Consultation Or call us directly: (262) 475-2615 · Hablamos Español